Over the past few years, I have ended up coming into contact with many computers belonging to individuals. My reason for doing so has varied, but usually I am helping them with something unrelated to security.
I found myself constantly saying the same things when I noticed bad security practices — “you really should update or remove Java”, “you need to actually stop clicking ‘Postpone’ and restart the computer some time”, “untick that box to install the toolbar” and so on.
Computer security is hard.
But, particularly when it comes to computers belonging to individuals, we have let the perfect become the enemy of the good. We have allowed anti-virus vendors to parrot messages about “total protection” instead of teaching sound principles and encouraging good practice.
Computer security, at least in this context, is in large part a human problem, not a technology problem.
So, a while ago, I had an idea to put together a really quick, 5-minute presentation that would encourage computer security principles that could dramatically lower the risk of individuals’ machines getting infected. I stripped it down to what I saw as the four most important principles (few enough that they might actually be remembered!):
- Keep software up-to-date — with emphasis on the importance of updates, despite the inconvenience, and mention the high-risk software titles du jour whose updates may not be entirely hands-off (Flash, Java, etc.).
- Keep up-to-date antivirus — with emphasis on such technology as the last line of defence, not ever a solution in and of itself.
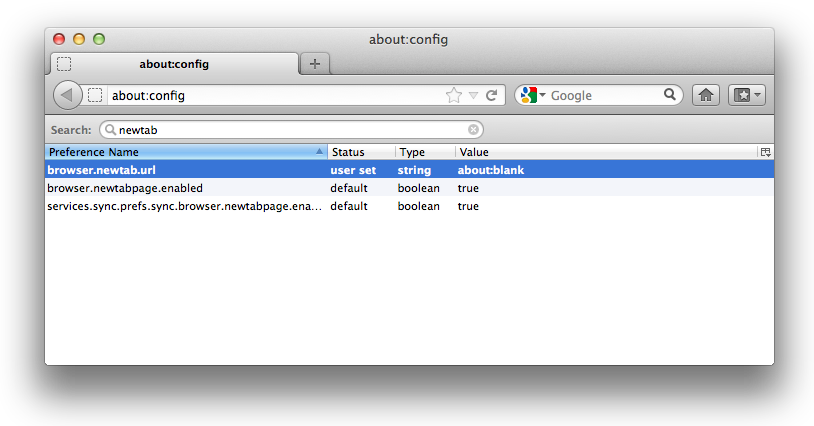
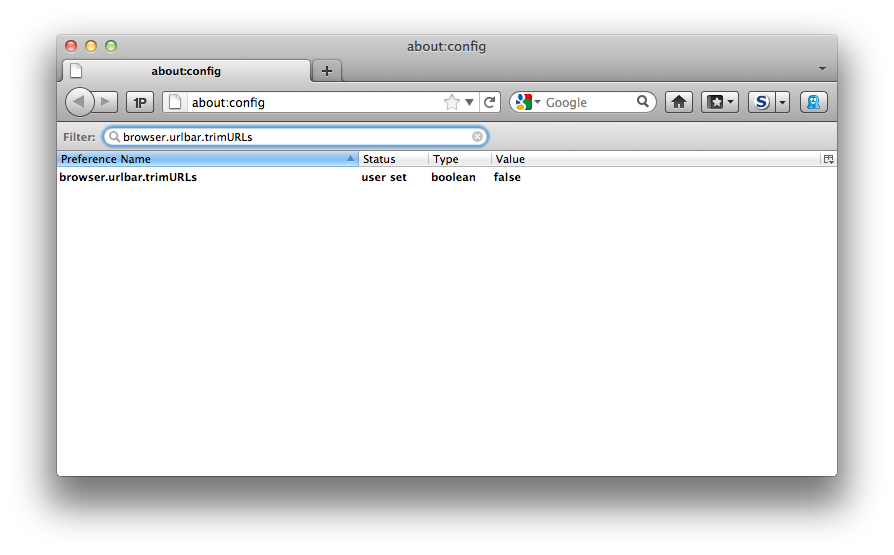
- Install software from trusted sources — perhaps the most important principle that requires behaviour change, this is about getting people to feel confident enough to build a trust model for software and then make informed decisions about each and every installation they make.
- Be suspicious — in particular about communications that invite clicking on things and so on, including using alternative channels to verify legitimacy of things that look suspicious (e.g. never clicking unexplained links!)
I’ve not given this talk yet, but I’d like to. It feels that computer security on home PCs is, in general, so awful, that even a very basic set of ideas that are memorable enough to implement can probably make a significant difference to the health of our personal information infrastructure.
I would welcome feedback from others on these slides, as well as the idea.
I think it is quite important to keep it to five minutes, make it concise enough that it will be memorable and actionable, but I’m sure this idea can (and needs to) evolve and improve over time.
If you would like to use the slides, feel free to do so under the Creative Commons BY-NC-SA 2.0 licence. It would be great if many people could hear this message.